Protecting the game from hacking: how to increase the security of the project
How to protect your product?
Protecting the game from hackingHow to protect your product? Protecting the game from hacking
Creating a game can take months or even years, and investment in development can reach millions of dollars. Therefore, when the main production is almost completed, you need to take care of the security of your project so that at some point it does not appear on public torrents.
In addition to fulfilling its main task, hacking protection should remain as invisible to gamers as possible. It must not be allowed to negatively affect the gameplay and cause a negative user experience.
For example, a complex registration process or authorization through a third-party application, as in the remake of Diablo II: Resurrected, is unlikely to cause positive emotions in a person. What’s more, in some cases, improving security will negatively affect the performance of the game and may cause technical problems, which is also unacceptable.
In this article, we will look at how to reliably protect the game, and at the same time not harm it.
Using special software
SoftwareUsing special software Software
To protect the client’s investment, many developers resort to the use of special software that supposedly guarantees reliable protection. However, in practice, things may not turn out so well.
A striking example in this sense is the Denuvo service. Immediately after the release of the technology on the market, its creators announced that it was simply impossible to hack their software.
A large-scale marketing campaign inspired confidence, and the product began to be used in many projects. As a result, all parties were in the red. After some time, pirated versions of games did appear, which negatively affected the profits of publishers, and gamers themselves were forced to put up with the fact that Denuvo reduces the performance of games even on powerful devices.
Is it possible to completely protect the game from hacking
Protecting the game from hackingIs it possible to completely protect the game from hacking Protecting the game from hacking
Game hackers are extremely resourceful. For example, for projects that are distributed on disks, they found several ways to bypass protection at once: the first is to replace system files so that the game no longer requires activation, and the second is to create a disk image in a virtual drive.
Even PlayStation games, which are authenticated automatically every few minutes on Sony servers, have also learned to be distributed in a pirated way. To do this, a person just needs to connect an account with a purchased game, download it to the console and turn off the Internet, after which the system will “think” that the user is just playing offline and will not turn on the lock.
With digital versions on a PC, everything is even easier – here the “specialists” also found a way to replace system files, run similar servers at a different IP address, and many more options for bypassing the license.
All this leads to the fact that many popular games are hacked very quickly. For example, From Software’s long-awaited Elden Ring could be downloaded for free within a few weeks of its release. However, this does not mean that there is no way to secure your investment, and one of the main ones is the provision of additional services that will only work if you purchase a licensed version of the game. Let’s look at a few examples:
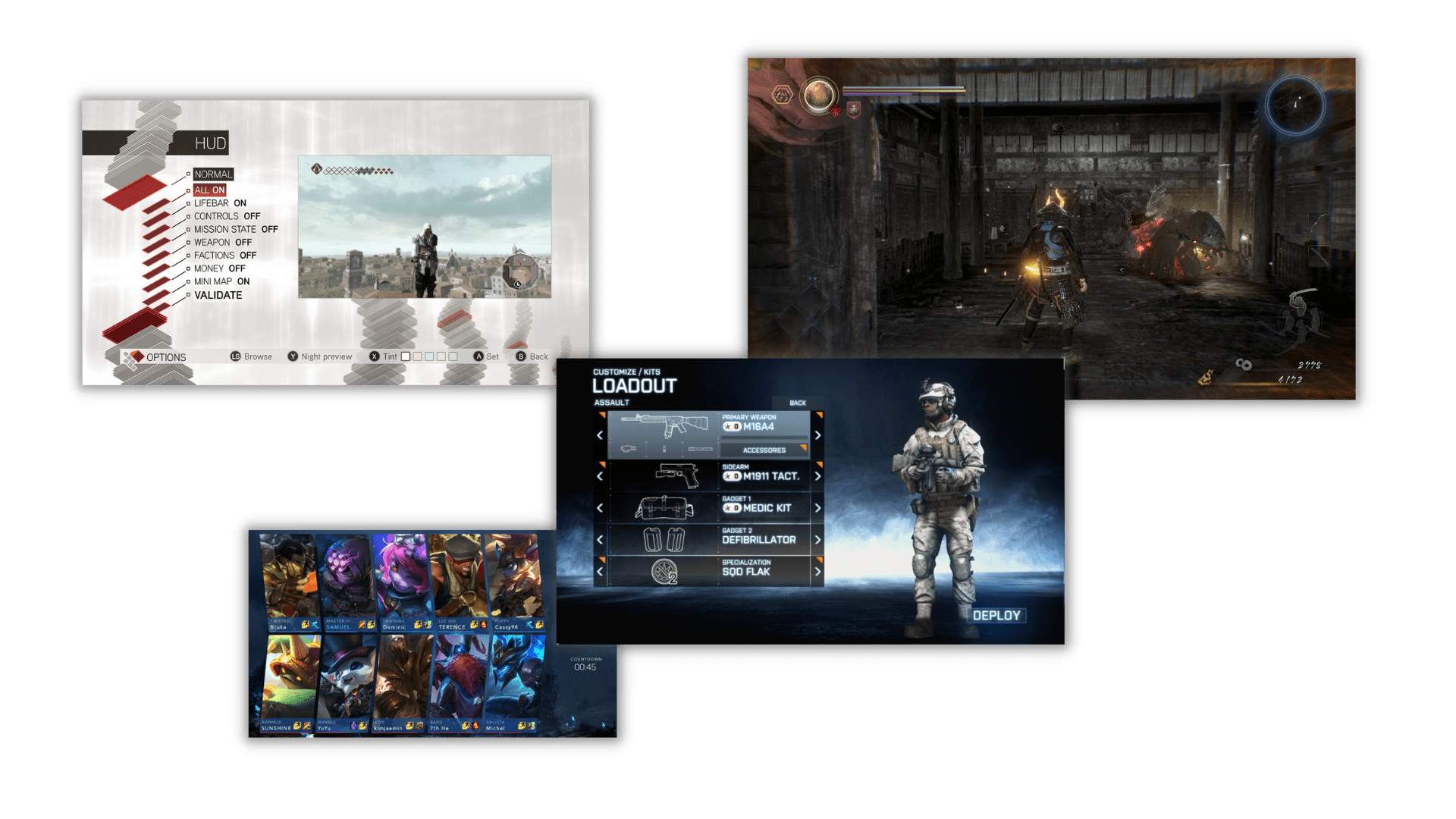
- Multiplayer and PvP. Increasingly, gamers prefer to play games not alone, but in the company of friends, or even compete with each other. Providing such an opportunity allowed the creators of the same Elden Ring to maintain their profits even despite the release of a pirated version.
- System of ratings and achievements. Achievements are only valuable if they are public and can be tracked and compared with the results of other users.
This motivates the gamer to develop the character and causes excitement, which drastically affects the perception of the gameplay.
- Record saves in the cloud. Sometimes a user plays from different devices, and the ability to continue from the right place each time will be a good motivation to purchase a licensed version of the project.
- Personalization. In-game items such as weapons, equipment, character skins, and more help gamers express themselves in the virtual world. To provide them with the possibility of personalization, you can create special stores with a mandatory check of the gaming license.
- Marketplace for custom mods. Some users who really liked the game can start creating their own mods – with additional locations, alternative gameplay options, etc. On the one hand, this can be blocked, but it is better to use it for your own purposes by creating a separate marketplace for them with a verification of the main gaming license.
- Updates and themed events. You can release additional patches with temporary events that will fill the game universe with a new atmosphere. Such events, as a rule, last for 1-2 weeks, so you don’t have to worry about hacking them, but the owners of the official version of the game will certainly be happy.
Note that the last point opens up another way for publishers to monetize the game – through the sale of season passes. At a minimum, this will help pay for the development of additional patches, but most likely will bring substantial profits. For example, many large projects use this approach: League of Legends, RAID: Shadow Legends, Call of Duty and many others.
Result
Result
Summing up, it must be said that protecting a game from piracy is a task not only for a programmer, but also for a game designer. A properly balanced project will force gamers to abandon the hacked versions themselves in order to get more emotions and impressions from the gameplay.
When developing games, we, at AVADA MEDIA, strive to protect the investments of our customers as much as possible and use all existing opportunities for this. To learn more about our approach, please contact us by filling out the feedback form.
Fresh works
We create space projectsFresh works
The best confirmation of our qualifications and professionalism are the stories of the success of our clients and the differences in their business before and after working with us.
Our clients
What they say about usOur clients What they say about us
Successful projects are created only by the team
Our teamSuccessful projects
are created only by the team Our team












Contact the experts
Have a question?Contact the experts Have a question?
-
Phone:+ 38 (097) 036 29 32
-
E-mail:info@avada-media.com.ua