Keeping digital funds is an important task for any cryptocurrency trader. Therefore, the choice of a crypto-wallet should be approached responsibly.
In this article, we will look at what types of crypto wallets exist, how they differ, and why you need to develop your own wallet when the market offers ready-made solutions.
Users often say they store cryptocurrency in wallets. But in reality it is not so. Digital assets are located on the blockchain, and a wallet is just a tool that gives a person access to a certain number of coins within a decentralized network and ensures their safe storage.
A crypto wallet itself is a special program that enables a person to interact with the blockchain: create payments, send transfers, store funds, etc. On the technical side, such software can be integrated with software, stock or hardware environments.
Regardless of the type of wallet, it necessarily contains two elements – private and public keys:
To simplify, the public key can be compared with the bank card number that you send to the counterparty to receive payment, and the private key with the pin code and CVV code.
When conducting a financial transaction, it is signed with a private key and then sent to the blockchain chain. After verification by the blockchain, the transaction is executed.
To order a crypto wallet, you need to understand what varieties they are. Globally, digital wallets can be divided into two types: custodian and non-custodian. Let’s consider each of them in more detail.
Custodian wallet
These are wallets in which the user’s beer and public keys, as well as all data about his transactions, are stored by a third party. Many consider this type of wallet to be unsafe and susceptible to hacking. But, at the same time, they make it possible to restore access to funds if the user has lost a password or a secret phrase.
Custodian wallets can be divided into:
Not a custodian wallet
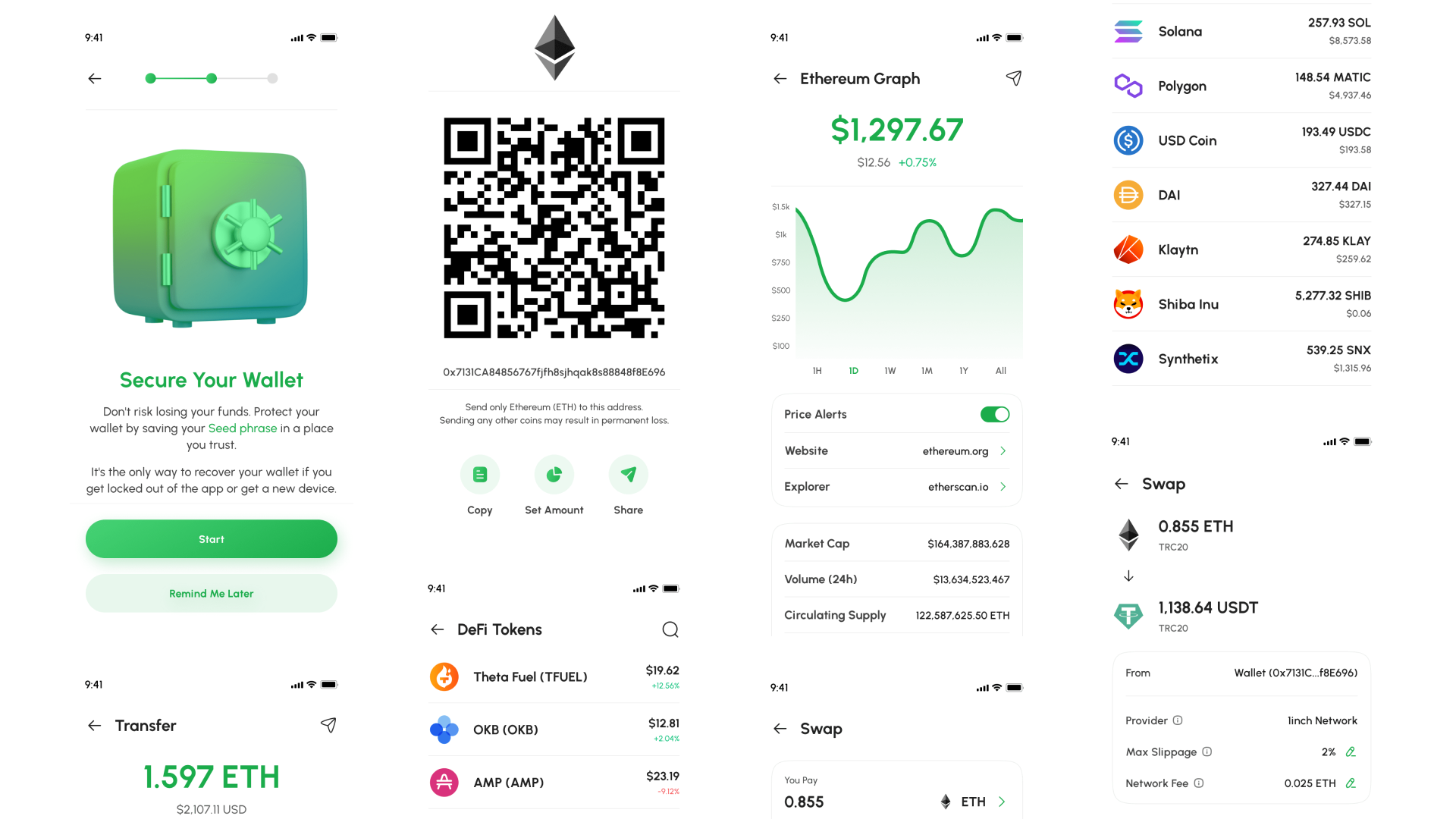
A type of wallets in which the keys belong directly to its owner and are not transferred to third parties. Of course, from a security point of view, such wallets are more reliable. But, at the same time, the user needs to take a responsible attitude to the storage of keys, because if they are lost, it will be impossible to get access to their money again.
Non-custodial wallets can be divided into:
In the crypto industry, there is one rule: everyone is responsible for his money himself. For example, in the real world, you can put money in a bank and be sure that it won’t go anywhere. This does not work with digital currency.
Choosing a wallet from those already on the market, you will have to choose a balance between convenience and security. The higher one parameter, the lower the other. And vice versa. Therefore, if you plan to store large amounts, we recommend ordering the development of a cryptocurrency wallet that will fully meet your needs.
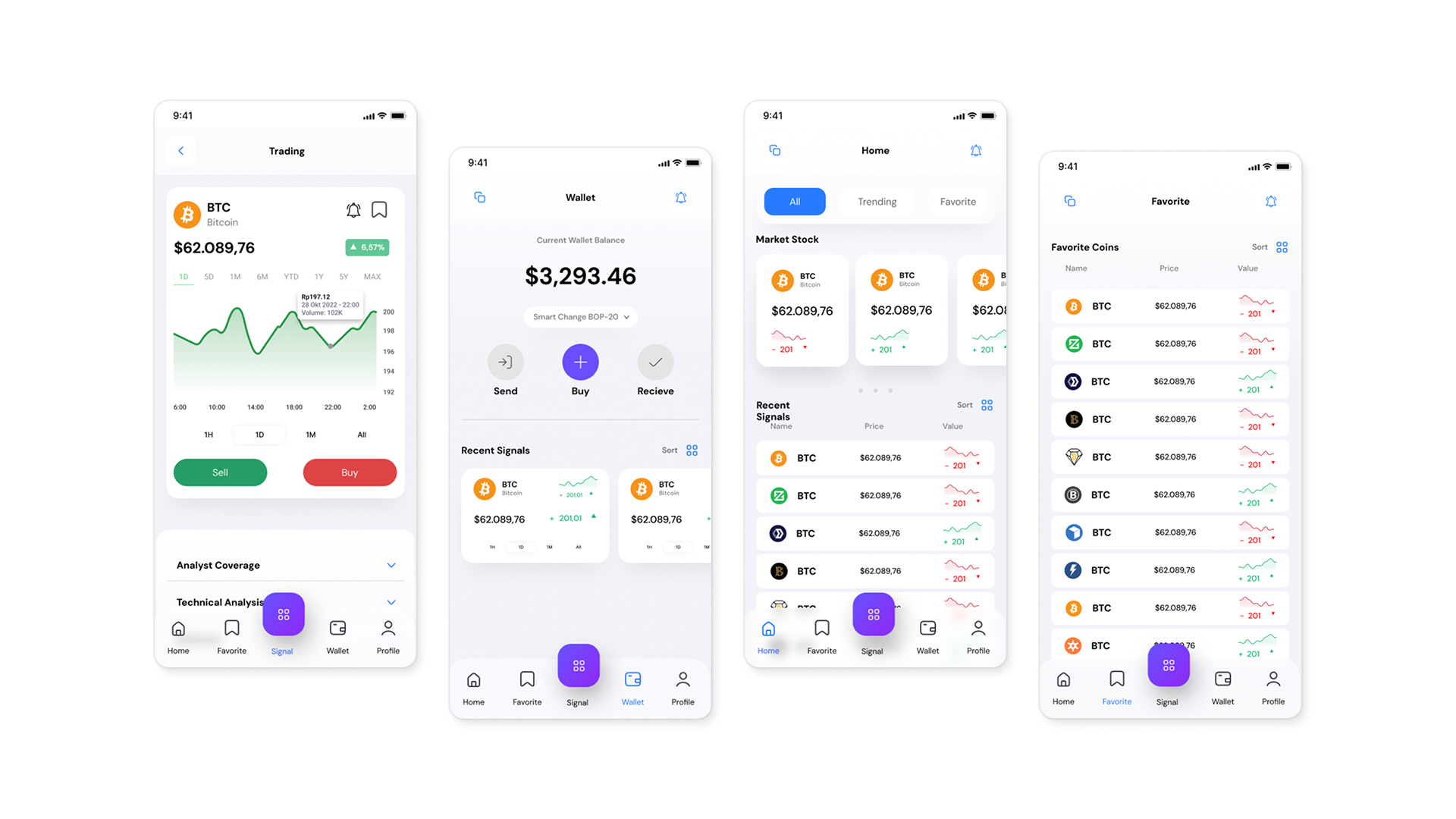
Using your own cryptocurrency management application opens up unlimited possibilities for the user. During the development process, you can implement not only the basic set of functions of the wallet, but also additional features, including:
It is important that using their own crypto wallet, the user does not overpay the commission. Therefore, the cost of developing such a solution will quickly pay off.

When ordering the creation of a crypto wallet in AVADA MEDIA, you can count on 9 years of experience of the studio staff in the field of blockchain development.
We will create:
Our employees use advanced technologies to ensure the maximum security, adaptability and speed of applications.
Our works
Contact the experts Have a question?
The user, filling out an application on the website https://avada-media.ua/ (hereinafter referred to as the Site), agrees to the terms of this Consent for the processing of personal data (hereinafter referred to as the Consent) in accordance with the Law of Ukraine “On the collection of personal data”. Acceptance of the offer of the Consent is the sending of an application from the Site or an order from the Operator by telephone of the Site.
The user gives his consent to the processing of his personal data with the following conditions:
1. This Consent is given to the processing of personal data both without and using automation tools.
2. Consent applies to the following information: name, phone, email.
3. Consent to the processing of personal data is given in order to provide the User with an answer to the application, further conclude and fulfill obligations under the contracts, provide customer support, inform about services that, in the opinion of the Operator, may be of interest to the User, conduct surveys and market research.
4. The User grants the Operator the right to carry out the following actions (operations) with personal data: collection, recording, systematization, accumulation, storage, clarification (updating, changing), use, depersonalization, blocking, deletion and destruction, transfer to third parties, with the consent of the subject of personal data and compliance with measures to protect personal data from unauthorized access.
5. Personal data is processed by the Operator until all necessary procedures are completed. Also, processing can be stopped at the request of the User by e-mail: info@avada-media.com.ua
6. The User confirms that by giving Consent, he acts freely, by his will and in his interest.
7. This Consent is valid indefinitely until the termination of the processing of personal data for the reasons specified in clause 5 of this document.
Send CV
Contact us in any convenient way for you:
+ 38 (097) 036 29 32